What Is Crypto Privacy?
Crypto privacy refers to the ability to keep transaction details — such as sender, receiver, and amount — confidential while still allowing blockchain networks to verify transactions.
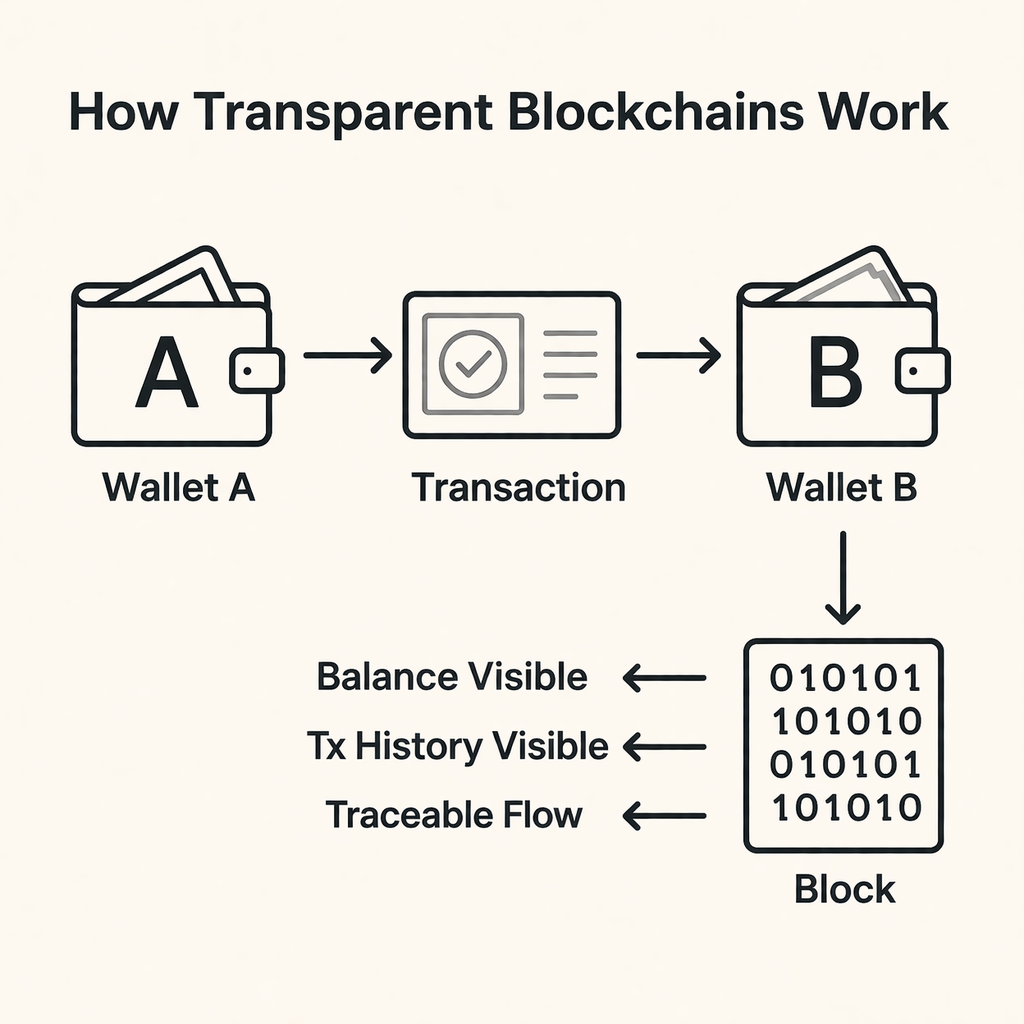
Most public blockchains, including Bitcoin and Ethereum, are fully transparent. This means wallet balances, transaction histories, and fund flows are visible to anyone, creating a fundamental contradiction: financial systems require confidentiality, but blockchains expose everything.
Why Crypto Privacy Is Becoming Critical
Crypto privacy has become a critical issue as blockchain moves beyond speculation into real financial use cases. From payroll and trade finance to stablecoin settlement and enterprise treasury management, full transparency increasingly conflicts with real-world financial requirements.
In This Guide:
- Why transparent ledgers create structural privacy risks
- The major cryptographic approaches behind modern crypto privacy
- Real-world applications where financial confidentiality is essential
- The technical challenges of implementing privacy on public blockchains
- How next-generation infrastructure enables scalable, compliant privacy payments
The Origins of Blockchain: Radical Transparency by Design
When Bitcoin launched in 2009, it introduced a permissionless public ledger where:
- Every transaction is permanently recorded
- Every wallet balance is publicly visible
- Every transfer path can be analyzed
This transparency model was revolutionary. It eliminated the need for trusted intermediaries and enabled global verification.
Later, Ethereum expanded this design to smart contracts, DeFi, and tokenized assets. The result: a fully observable financial system.
But transparency at scale creates unintended consequences.
The Problem: Why Transparency Undermines Crypto Privacy
In traditional banking systems, transaction details are typically visible only to the sender, the recipient, and the financial institution facilitating the transfer. Financial confidentiality is protected by regulation, internal controls, and private databases.
In contrast, most public blockchains operate on fully transparent ledgers where anyone can:
- View wallet balances
- Track payment history
- Analyze transaction relationships
- Map business activity
Although wallet addresses are pseudonymous, modern blockchain analytics platforms can often reconstruct real-world identities. Companies such as Chainalysis, Arkham, and Nansen use techniques like address clustering, transaction pattern analysis, and behavioral profiling to connect wallet activity to individuals, businesses, or institutions. Over time, pseudonymous addresses can effectively become identifiable financial profiles.
Another challenge is the permanence of blockchain data. Transactions recorded today remain publicly accessible indefinitely, meaning that financial relationships, business payments, or asset holdings could potentially be analyzed years later as analytics tools become more advanced.
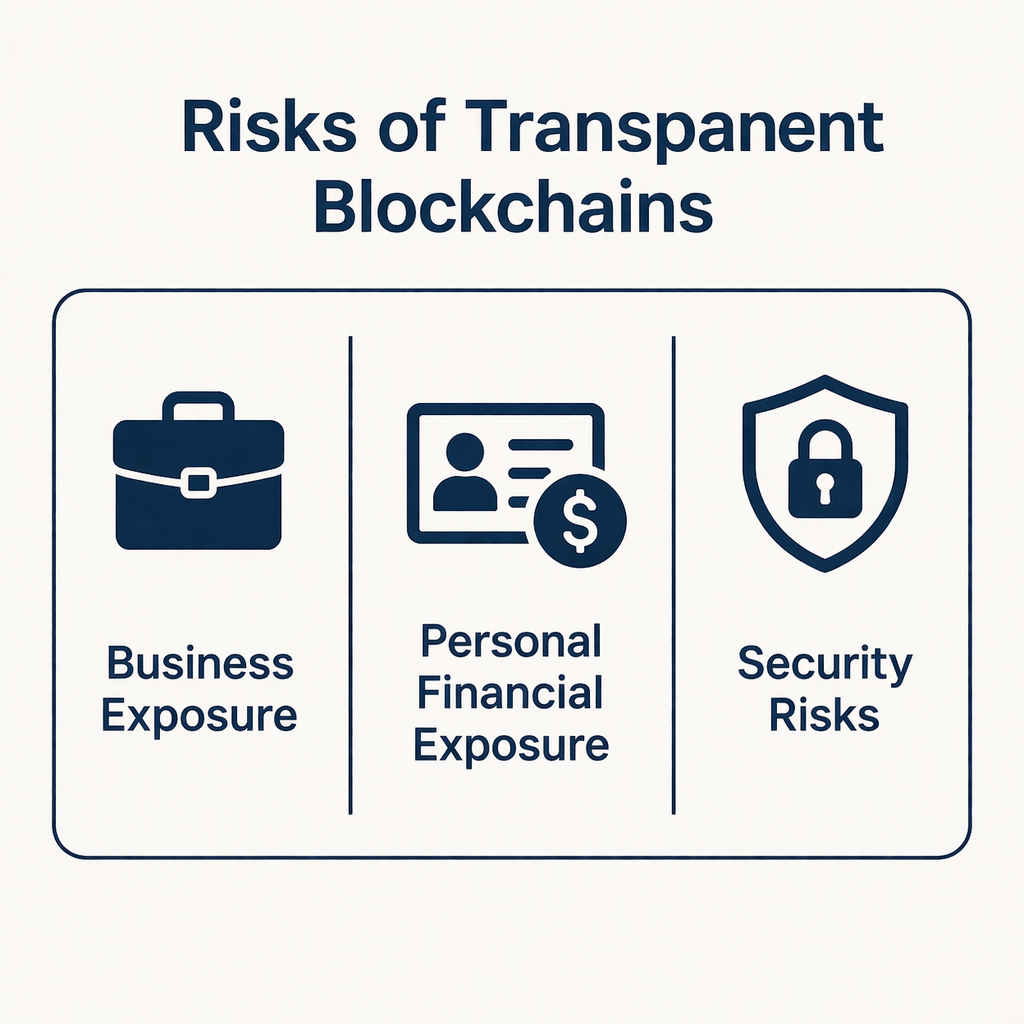
This level of transparency creates several real-world risks:
- Competitive Intelligence Risk Businesses paying suppliers in crypto may unintentionally reveal transaction volumes, counterparties, and supply-chain relationships to competitors.
- Personal Financial Exposure Individuals receiving salaries, freelance payments, or on-chain income may expose their financial history to anyone capable of tracing their wallet.
- Targeting and Security Threats Public wallet balances can make high-value holders visible targets for phishing attacks, social engineering, or physical threats.
As crypto evolves from speculative trading infrastructure into real financial rails for payroll, global commerce, and stablecoin settlement, protecting sensitive financial information has become a fundamental requirement for the next generation of blockchain systems.
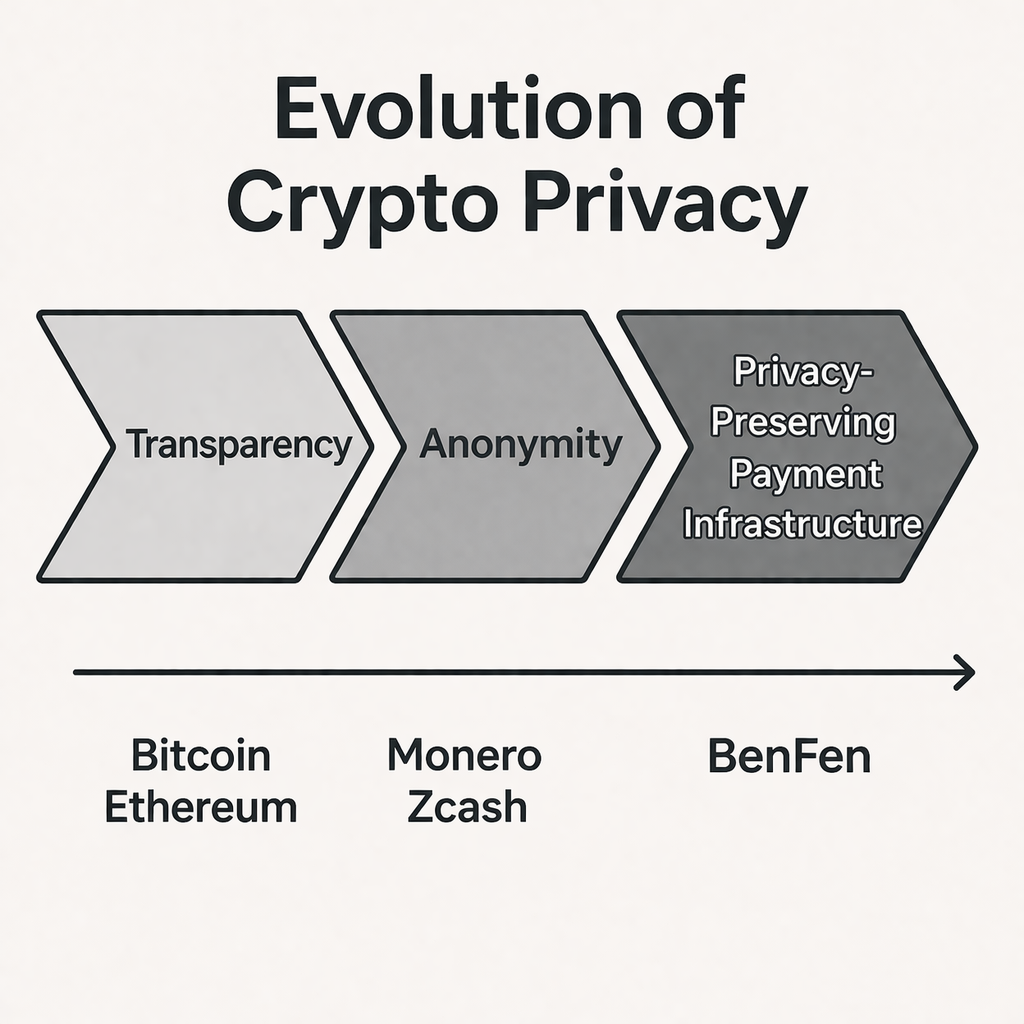
The Evolution of Crypto Privacy Technologies
As the limitations of fully transparent blockchains became more apparent, developers began exploring ways to introduce privacy into decentralized systems. Over time, multiple cryptographic approaches emerged, each attempting to balance confidentiality, security, and verifiability.
Rather than relying on a single technique, modern crypto privacy research spans a wide range of cryptographic tools designed to protect sensitive financial data while preserving the integrity of blockchain networks.
These technologies represent the gradual evolution of crypto privacy — from early anonymity-focused networks to more advanced privacy-preserving infrastructure capable of supporting real-world financial applications.
Privacy Coins: Monero and Zcash
To address the privacy risks of transparent blockchains, early privacy-focused networks emerged, most notably Monero and Zcash. These projects attempted to introduce confidentiality directly into blockchain transactions while preserving decentralized verification.
These networks introduced several important cryptographic technologies, including:
- Ring signatures
- zk-SNARKs (zero-knowledge proofs)
- Shielded transactions
Although both Monero and Zcash aim to protect financial privacy, they use different technical approaches:
- Monero relies on ring signatures, stealth addresses, and confidential transactions to obscure the sender’s identity and transaction flow. When a transaction is created, it is grouped with several other possible senders in a “ring,” making it extremely difficult for observers to determine which participant actually initiated the payment.
- Zcash, on the other hand, uses zero-knowledge proof systems known as zk-SNARKs. These cryptographic proofs allow transactions to be validated without revealing key details such as the sender, receiver, or transaction amount. In so-called shielded transactions, all sensitive financial information remains hidden while still allowing the network to verify the transaction’s validity.
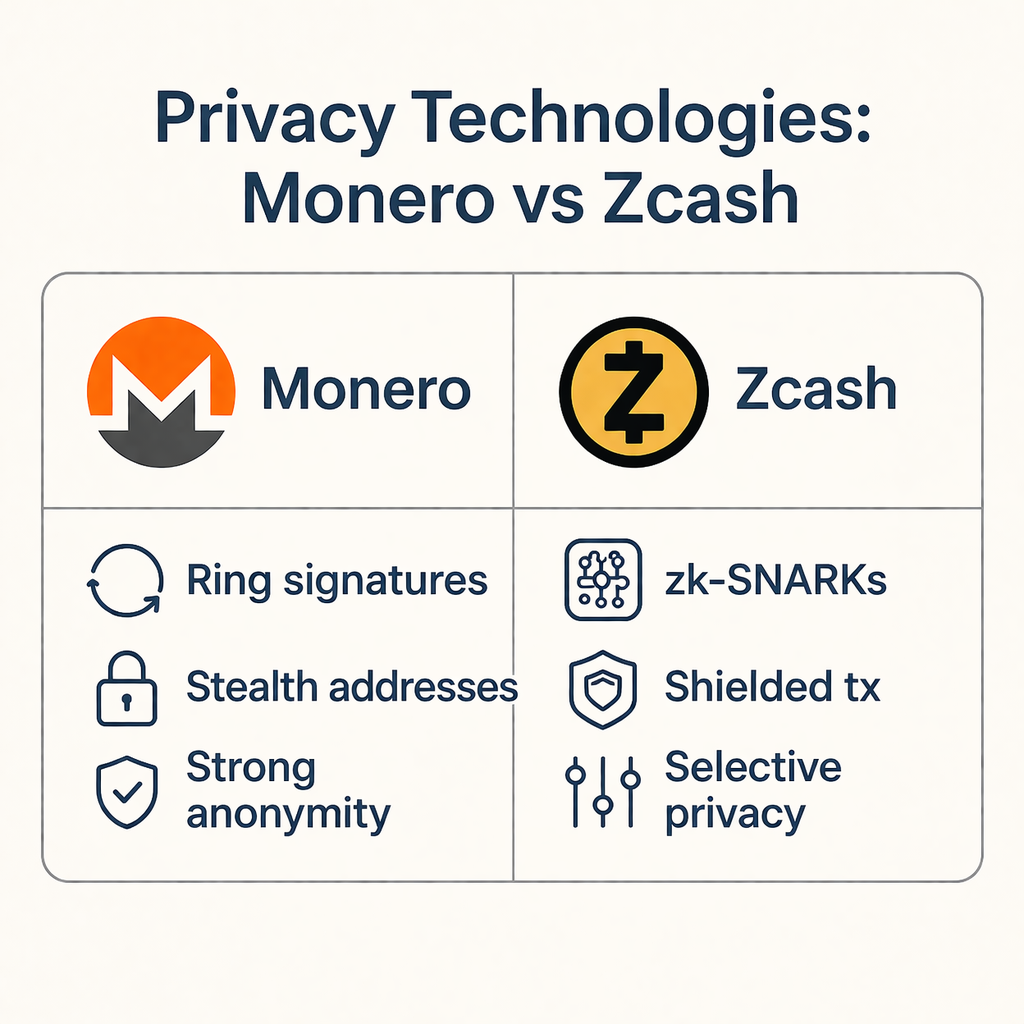
These technologies demonstrated that confidential blockchain transactions were technically possible. However, despite their strong privacy guarantees, adoption remained limited for several reasons:
- Liquidity fragmentation
- Regulatory ambiguity
- Weak DeFi integration
- Exchange delistings in multiple jurisdictions
Many regulators viewed fully anonymous transactions with caution, which led several major exchanges to restrict or delist privacy coins. As a result, these networks often operated in relatively isolated ecosystems with limited interoperability.
Privacy coins successfully proved the feasibility of on-chain anonymity, but mainstream financial systems require a slightly different balance — one that combines privacy with accountability.
Enterprises, payment providers, and financial institutions typically require confidentiality with auditability, meaning sensitive transaction data should remain private while still allowing regulatory oversight when necessary.
For crypto privacy to support large-scale financial infrastructure, the next generation of solutions must reconcile several requirements simultaneously:
- Enterprise compliance
- Regulatory access
- High throughput
- Seamless user experience
This shift marks the transition from early privacy experiments toward a new phase of privacy-preserving financial infrastructure.
Cryptographic Approaches Behind Crypto Privacy
Beyond early privacy coins, the broader field of crypto privacy relies on several cryptographic approaches designed to protect sensitive transaction data while maintaining blockchain verifiability.
Different technologies address different aspects of privacy, such as hiding the sender, concealing transaction amounts, or enabling computation on encrypted data. Each method offers unique advantages but also introduces technical trade-offs in terms of scalability, performance, and complexity.
The most widely discussed privacy technologies in blockchain systems include:
| Technology | Purpose | Key Challenge |
| Ring Signatures | Obscure the identity of the transaction sender by mixing it with other possible signers | Larger transaction sizes and increased verification costs |
| Zero-Knowledge Proofs | Allow transactions to be validated without revealing sensitive information such as sender, receiver, or amount | High computational overhead for proof generation |
| Secure Multi-Party Computation (MPC) | Enables multiple participants to jointly compute results without revealing their individual data | Coordination complexity and communication overhead |
| Fully Homomorphic Encryption (FHE) | Allows computation to be performed directly on encrypted data | Extremely high computational cost in current implementations |
These cryptographic primitives form the technical foundation of modern privacy-preserving blockchain systems. Rather than relying solely on anonymity, newer architectures increasingly combine multiple techniques to achieve confidentiality, scalability, and regulatory compatibility. Different technologies do not replace each other but form a combined architecture in different scenarios, which is also the core direction of the current evolution of privacy infrastructure.

Regulatory Challenges of Crypto Privacy
As crypto privacy technologies evolve, regulatory considerations have become increasingly important.
Financial authorities around the world have expressed concerns about fully anonymous transactions, particularly in relation to anti-money laundering (AML) and counter-terrorism financing (CTF) requirements.
Frameworks such as the FATF Travel Rule require financial institutions to collect and share transaction information under certain conditions, which presents challenges for purely anonymous blockchain systems.
As a result, several privacy-focused cryptocurrencies have faced exchange delistings or restricted access in certain jurisdictions.
However, it is important to distinguish between anonymity and confidentiality.
Modern crypto privacy solutions are increasingly designed to support selective disclosure, allowing sensitive transaction data to remain private while still enabling regulatory access when legally required. This shift reflects a broader industry trend toward compliant privacy, where blockchain systems can balance user confidentiality with institutional and regulatory requirements.
BenFen Public Chain: A Privacy-Native Infrastructure for Crypto Privacy
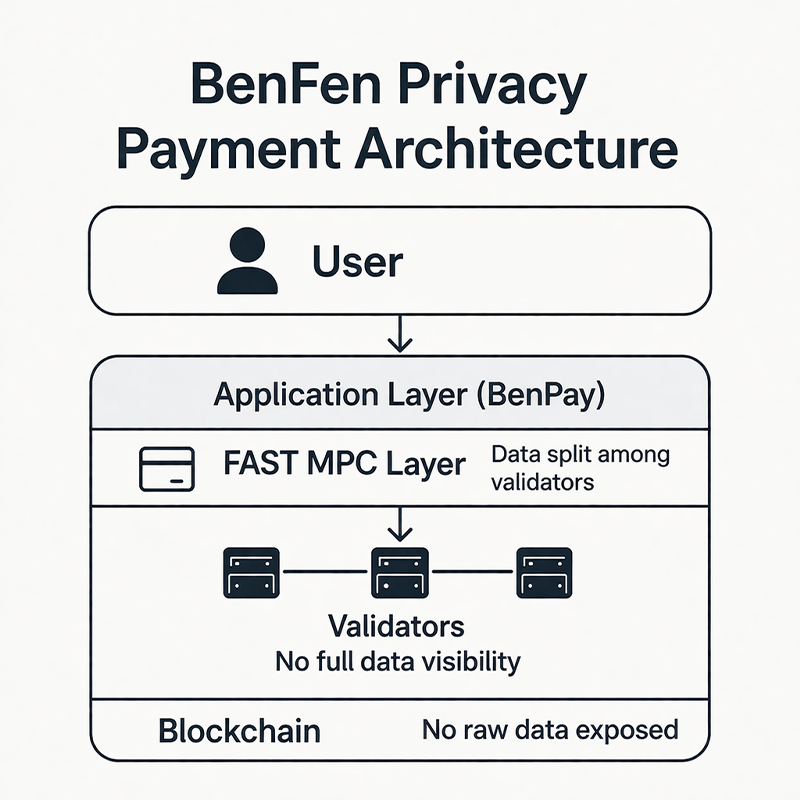
Driven by the above-mentioned technical paths and practical demands, a new generation of privacy payment infrastructure has begun to emerge. The BenFen public chain is designed to support privacy-enhanced payment applications while remaining compatible with broader Web3 ecosystems. Instead of forcing users into isolated privacy networks, BenFen focuses on building a privacy-native infrastructure that integrates seamlessly with real-world financial use cases.
At the application layer, this capability is implemented through BenPay, enabling users to directly utilize privacy protection functions in actual payment scenarios without having to understand the underlying complex cryptographic mechanisms.
Privacy-Ready Payment Architecture
Unlike traditional public blockchains, where transaction data is fully exposed by default, BenFen minimizes data leakage at both the protocol and application layers.
One of the key technologies enabling this is FAST MPC (Secure Multi-Party Computation).
Instead of exposing transaction values directly on-chain, FAST MPC splits financial data into encrypted shares that are jointly processed by network validators. Each validator only has access to a fragment of the data, ensuring that no single participant can reconstruct the full transaction details.
This architecture allows transactions to be verified collaboratively while keeping sensitive information — such as balances, payment amounts, and counterparties — confidential.
BenFen’s FAST MPC framework is also optimized specifically for payment-scale performance — supports second-level transaction confirmation and high TPS under full privacy encryption, without sacrificing throughput. Unlike general-purpose MPC implementations, FAST MPC minimizes computational overhead so that privacy protection does not introduce latency at the application layer.
As a result, BenFen enables confidential transactions by design, rather than relying on external privacy layers or optional shielding mechanisms.
Enterprise & Consumer Use Cases
By combining privacy with performance, BenFen supports a wide range of real-world payment scenarios, including:
- Cross-border settlements
- Payroll distribution
- Merchant payments
- Web3-native business operations
In these contexts, financial confidentiality is not optional. Businesses need to protect transaction flows, salary data, and commercial relationships, while individuals expect their financial activity to remain private.
BenFen’s architecture enables these use cases without sacrificing usability or transaction efficiency.
Integrated Ecosystem Support
In the BenFen ecosystem, privacy capabilities are deeply embedded throughout the entire on-chain financial system and can be seamlessly integrated with the following modules in the future and made available to users through the BenPay App:
- DeFi protocols
- RWA (Real-World Asset) tokenization
- Stablecoin-based financial systems
- On-chain treasury and settlement tools
This interoperability ensures that privacy-preserving transactions can function within a complete financial stack, rather than existing in siloed environments like earlier privacy-focused networks.
From Privacy Feature to Financial Infrastructure
By embedding confidentiality directly into transaction processing, BenFen shifts crypto privacy from a niche technical capability to a practical financial primitive.
Rather than prioritizing full anonymity, the network is designed to support confidentiality with scalability and real-world usability — a model better aligned with enterprise adoption and institutional requirements.
This approach represents the next stage in the evolution of crypto privacy: moving beyond isolated privacy coins toward integrated, high-performance infrastructure capable of supporting global financial activity.
From Transparent Ledgers to Confidential Payments
The evolution of crypto privacy can be summarized in three stages:
| Stage | Focus | Limitation |
| Early Blockchain (Bitcoin, Ethereum) | Full transparency | Financial exposure |
| Privacy Coins (Monero, Zcash) | Strong anonymity | Limited adoption |
| Next-Gen Infrastructure (BenFen) | Confidential & usable privacy | Scalable integration |
We are now entering the third phase — where privacy is built into payment systems by design, not added as an afterthought.
Why Crypto Privacy Matters for the Future of Web3
As crypto integrates into real-world finance, privacy becomes critical for:
- Institutional adoption
- Enterprise treasury operations
- Freelancers and global payroll
- Cross-border commerce
- Stablecoin-based payments
Without crypto privacy, blockchain risks becoming a surveillance ledger rather than a financial innovation.
With confidential payment infrastructure like the BenFen public chain, Web3 can maintain transparency where necessary — while protecting sensitive financial data where appropriate.
Conclusion: Crypto Privacy Is the Next Infrastructure Layer
Crypto began as a radically transparent experiment. It is now evolving into a mature financial system. The next phase is not about hiding activity — it’s about enabling secure, confidential, and compliant payments. Crypto privacy is no longer an add-on feature. It is becoming a foundational requirement for scalable digital finance.
As infrastructure like the BenFen blockchain continues to develop privacy-ready payment systems, the industry moves closer to a future where blockchain is both trustless and discreet — maintaining transparency in principle and keeping private when necessary. This will become the default paradigm for the next-generation blockchain financial system.
Learn more about BenFen’s privacy payment infrastructure:
The shift from transparent ledgers to privacy-preserving payments is crucial as crypto moves into enterprise use cases where financial confidentiality isn’t just preferred but necessary. It’s fascinating to see how cryptographic innovations are being applied to maintain trust without sacrificing privacy. This evolution will likely shape how we think about financial transparency in the broader Web3 ecosystem.
The shift towards privacy-preserving solutions is crucial as blockchain moves into real-world applications like payroll and trade finance. Privacy isn’t just about user anonymity, but also about meeting legal and regulatory standards. It’s exciting to see how cryptographic solutions will address these challenges.