Blockchain’s greatest strength is its transparency, but in payment and financial scenarios, this becomes its biggest weakness. When all transaction data is publicly visible, business privacy and user security become hard to protect. As blockchain evolves from an “open ledger” to a “privacy‑payment infrastructure,”Multi‑Party Computation (MPC) has become one of the key technologies connecting cryptography and the distributed ledger.
This article systematically dissects the role of MPC in blockchain, including:
- The core principles and cryptographic components of MPC
- MPC’s key application scenarios in blockchain
- The protocol‑layer evolution of MPC blockchains
- Future trends of MPC + blockchain
- And a real‑world case of MPC in a stablecoin-payment‑oriented public chain
What is MPC Multi‑Party Computation?
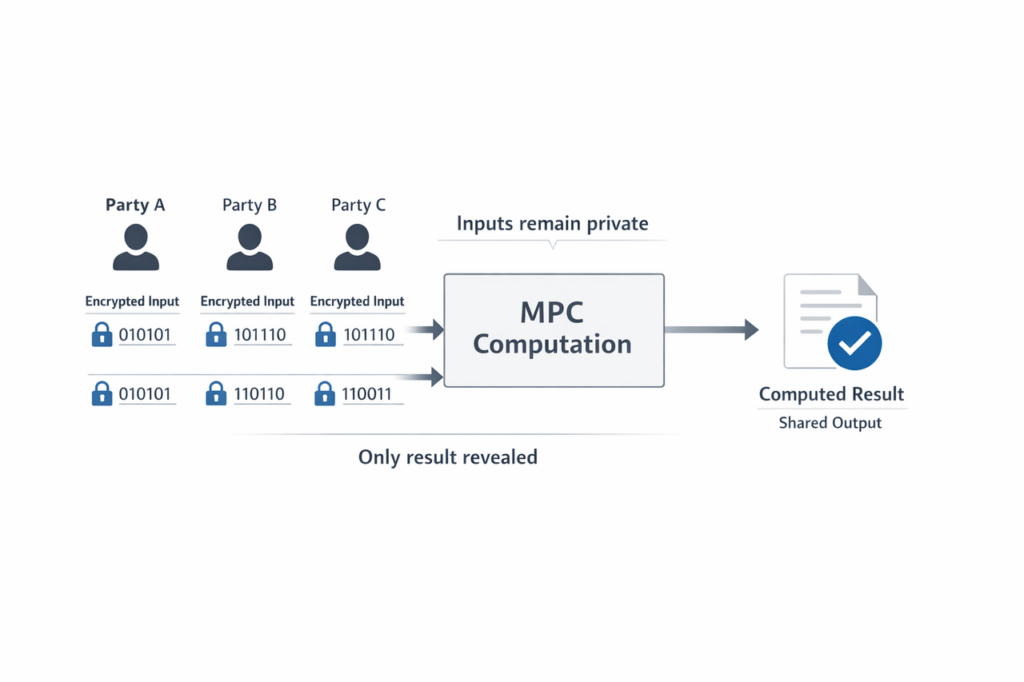
Multi‑Party Computation (MPC) allows multiple participants to jointly complete a computation task without revealing their private inputs, finally outputting only the computation result and not exposing any party’s original data. This can be understood as: “Data remains private, but the computation result is jointly verifiable.“
Typical examples include:
- Multiple parties jointly calculating the average salary without revealing individual incomes;
- Multiple institutions jointly training an AI model (privacy AI / federated learning) without sharing raw data;
- Multiple nodes collaboratively computing a blockchain signature, instead of one single node holding the full private key.
Core Cryptographic Components of MPC
In a secure multiparty computation blockchain, MPC is typically used in conjunction with the following techniques:
- Secret Sharing: For example, Shamir’s Secret Sharing, which splits a key into multiple shares; several shares are required to reconstruct it.
- Threshold Signature (TSS): A signature can be generated once a sufficient number of nodes reach the threshold.
- Fully Homomorphic Encryption (FHE): Enables direct computation in an encrypted state.
- Zero‑Knowledge Proof (ZKP): Proves that a computation is correct, without revealing the underlying data.
These technologies together form the infrastructure of blockchain privacy computation, turning MPC from an “algorithm” into a “system‑level capability.”
Main Application Scenarios of MPC in Blockchain
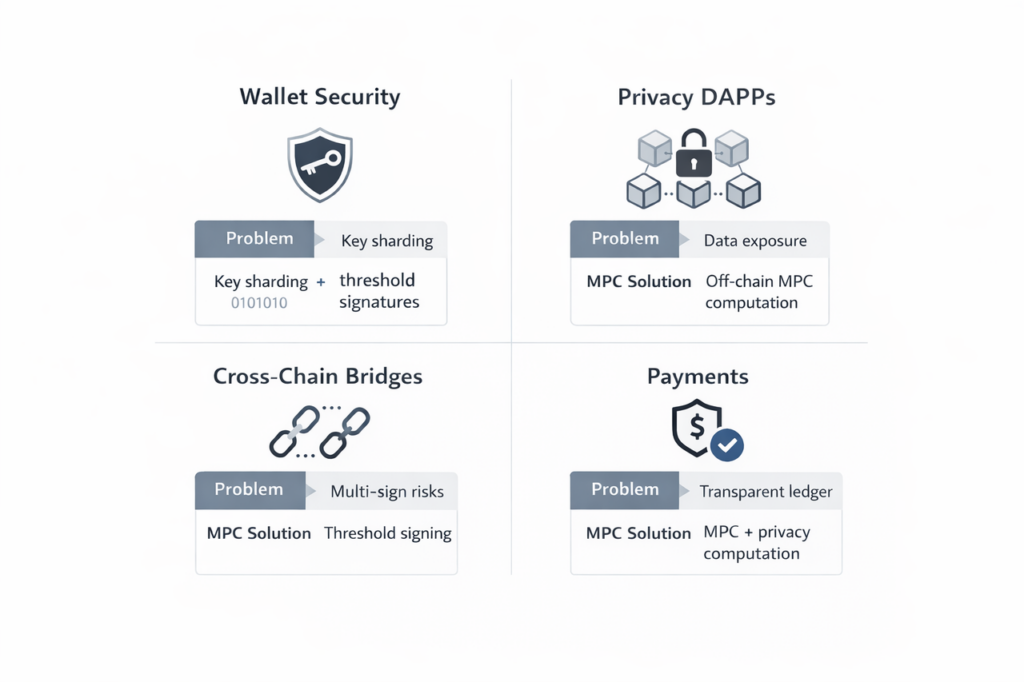
Core Comparison of Multi-Party Computation Use Cases
From a practical standpoint, MPC is no longer limited to a single security module, but is gradually evolving into a universal foundational capability covering wallets, cross‑chain bridges, payments, and data computation. The following table compares MPC’s core value in different blockchain contexts:
| Application direction | Problems in traditional approaches | MPC‑based solutions | Core value |
| Wallet & private key management | Single‑point private key easy to leak | Key sharding + threshold signatures | Eliminates single‑point risk |
| Privacy‑computing DApps | Data must be public or rely on trusted third parties | Off‑chain MPC + on‑chain verification | Data never leaves local nodes |
| Cross‑chain bridges | Multi‑sign or centralized‑validation risks | MPC‑based threshold signing | Improves cross‑chain security |
| Payment systems | Transparent ledger exposes transaction details | MPC + privacy computation | Protects business privacy |
- MPC Wallets and Private Key Management
Traditional “single private key + seed phrase” schemes have serious single‑point risks. MPC wallets adopt “key sharding + threshold signatures,” changing the role of keys from “being held” into “collaboratively computed signatures.”
- Private keys are split into multiple shares when generated and held by different devices or nodes.
- When initiating a transaction, multiple nodes collaborate via an MPC protocol to jointly output a valid on‑chain signature.
- As long as the number of compromised nodes stays below the threshold, the private key remains unrecoverable.
Such schemes are widely used in institutional wallets, custodial systems, and cross‑chain bridge signatures, significantly reducing the “hot‑wallet single‑point explosion” risk.
- Privacy DApps and Privacy Computation on Blockchain
In DeFi, NFTs, DAOs, credit scoring, and privacy marketing, MPC can be combined with smart contracts to realize:
- Off‑chain privacy computation: Sensitive data (amounts, identities, addresses, etc.) is computed off‑chain, with only results or hashes submitted to the chain.
- Privacy voting and governance: The final voting result is computed without exposing any individual’s choice.
- Joint risk control and privacy‑centric credit scoring: Multiple institutions jointly train models or compute credit scores without sharing raw data.
The “MPC + smart contract” pattern is becoming one of the standard architectures for privacy‑centric DApps.
- MPC‑Based Signatures in Cross‑Chain bridges
Cross‑chain bridges typically rely on a group of “signing nodes” to validate and sign cross‑chain messages. When MPC is introduced:
- Private keys are split into multiple shares, each node holds only a part;
- MPC protocols collaboratively generate valid on‑chain signatures (e.g., ECDSA, BLS);
- Even if an attacker controls some nodes, forging a valid signature becomes computationally infeasible;
This “MPC + cross‑chain signing” pattern has become an important direction for next‑generation bridge and multichain message infrastructure.
- MPC‑Based Privacy Payments
In payment systems built on public blockchains, the transparent ledger exposes transaction details such as amount and counterparty information. By integrating MPC‑based privacy computation, payment‑focused chains can hide sensitive payment data while still enabling auditability and regulatory compliance.
Typical techniques include:
- Off‑chain MPC computation of encrypted payment metadata;
- On‑chain verification of encrypted or hashed results;
- Regulator‑controlled disclosure mechanisms for compliance checks.
These designs enable privacy‑preserving, high‑throughput payments, forming the backbone of MPC‑native payment blockchains.
Deep Integration of MPC with the Blockchain Protocol Layer
MPC is evolving from a “wallet‑layer add‑on” into a “chain‑layer infrastructure,” reflected in several directions:
- Off‑Chain Computation + On‑Chain Verification
On mainstream chains such as Ethereum, Solana, Aptos, and Sui, a common pattern is:
- MPC executes sensitive data computation off‑chain (such as risk control, credit scoring, and multi‑party data fusion).
- The computation result is submitted to on‑chain contracts in the form of hashes or encrypted data.
- On‑chain logic or ZKP mechanisms verify correctness without exposing the raw data.
This “off‑chain MPC + on‑chain contract” architecture preserves privacy while retaining the blockchain’s public verifiability.
- Convergence of MPC with ZKP and AI
The combination of MPC, ZKP, and federated learning is giving rise to more complex privacy‑AI and blockchain applications:
- MPC + ZKP: MPC protects raw data privacy, while ZKP proves that the computation logic is correct on‑chain.
- MPC + AI / Federated learning: Multiple institutions train models jointly on their private data, then deploy privacy‑protected model results onto the blockchain.
Such “MPC + ZKP + blockchain” combinations are expected to become standard architectures for high‑compliance sectors such as finance, healthcare, and government.
Future Trends of Multi‑Party Computation Blockchains
Combining technological progress and industry needs, the convergence of MPC and blockchain exhibits several clear trends:
- From “Wallet Layer” to “Full‑Stack Privacy Layer”
Currently, MPC mainly focuses on wallets, custody, and signatures. In the future, it will gradually expand to:
- Data layer: Privacy‑preserving storage and off‑chain privacy databases;
- Consensus layer: Decentralized signature committees based on MPC;
- Application layer: Privacy‑centric DeFi, DAO, NFT, etc.
Ultimately, MPC will form a complete privacy stack—from signatures to data, and then to applications—making it one of the core pillars of multi‑party computation blockchains.
- Co‑Optimization with Hardware and Cloud
MPC is sensitive to computational overhead and network latency, so:
- Hardware accelerators such as TEEs and secure chips will be closely integrated with MPC protocols.
- Lightweight MPC protocols will run efficiently on mobile devices and browsers.
- Cloud‑chain “MPC compute node clusters” may become standardized infrastructure services.
These optimizations will determine whether MPC can scale to high‑throughput blockchain scenarios or remain limited to niche security use cases.
Case: Embedding MPC into the Layer‑1 Stablecoin Payment Blockchain
Among the different implementation paths of multi‑party computation blockchains, BenFen Chain provides a design that integrates privacy‑computation capabilities with high‑performance payment‑oriented use cases at the protocol layer.
Its privacy payment system adopts a FAST‑MPC‑based confidential transaction architecture with regulatory oversight, integrating Block Nodes, FAST MPC, and a Regulator component to enable asset transfers in which “data is usable but not visible,” while delivering high throughput and low latency.
Unlike designs that treat MPC as a “wallet or external module,” BenFen embeds privacy computation directly into the chain layer, making it an integral part of the payment system rather than an add‑on.
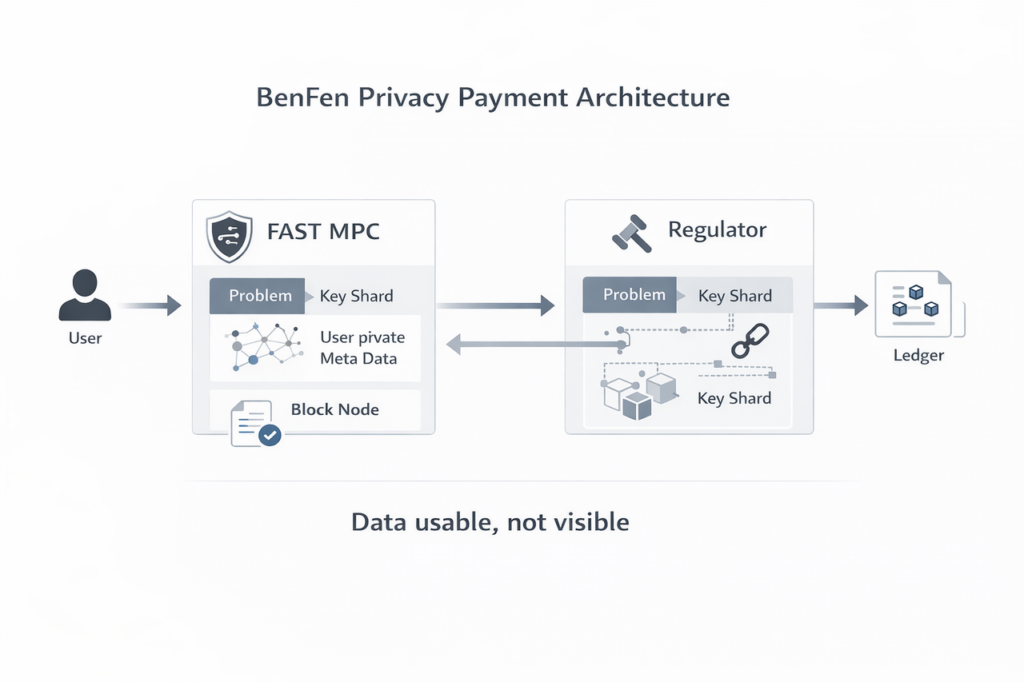
- Block Node: The foundation layer of on‑chain transactions
Block Nodes are responsible for transaction validation, consensus, and storage, forming the basic network layer of the system. Whether it is a plain transfer (Plain Tx) or a confidential transaction (Confidential TX), all transactions must pass through the Block Node, which therefore serves both the ledger‑layer role and the execution entry point for privacy‑protected transactions.
- FAST MPC: The core engine for privacy transactions
FAST MPC is the core technology that enables privacy protection in this architecture. It allows participants to jointly compute a predefined function over their private inputs without revealing the inputs, and the scheme is specifically optimized for high‑throughput blockchain environments. The MPC module runs inside the Block Node and mainly handles Key Shard and User Private Meta Data, used to generate or verify confidential transactions.
- Key Shard: The key to data security and regulatory intervention
The system encrypts or splits users’ private meta data into multiple key shards, which are held by different entities such as Block Nodes and Regulators. Only when key shards from different sources (for example, those held by a Block Node and a Regulator) are aggregated together can the core User Private Meta Data be accessed or decrypted. This design enhances data security while preserving a technical entry point for compliance audits.
- Regulatory oversight and controlled disclosure
BenFen’s architecture is not an “absolute black box.” Instead, it emphasizes regulatable and auditable privacy payments. When audits or compliance checks are required, the Regulator can be authorized to trigger a disclosure workflow, gathering relevant key shards from Block Nodes to access only specific transaction data in a controlled and auditable manner.
- Native integration of MPC threshold signatures (TSS)
BenFen natively supports MPC threshold signature (TSS) technology at the chain layer. This means that:
- Private keys are never reconstructed in full: From key generation, storage, to transaction signing, private keys are always maintained as “shards” across decentralized validator nodes;
- High‑speed payment experience: By optimizing the communication rounds of the TSS algorithm, BenFen achieves millisecond‑level transaction confirmation, sufficient to support the on‑chain payment scenarios of BenPay, the payment ecosystem built on BenFen.
- Privacy enhancements in the payment layer (in collaboration with TX‑SHIELD)
Through deep integration with the TX‑SHIELD privacy‑infrastructure platform, BenFen adds higher‑dimensional security protections to payment scenarios:
- Data desensitization of accounts and amounts: Under compliance‑friendly constraints, MPC‑based collaborative computation is used to execute payment logic, avoiding the exposure of sensitive business information that would occur on a fully transparent ledger;
- “Invisible safeguards” for asset security: Even if a single payment node is compromised, attackers cannot forge signatures alone because each node only holds a key shard, thereby safeguarding users’ assets at the root level.
- Future evolution: from FAST MPC to SMPC and FHE
In the next stage, this type of architecture can evolve into a more decentralized SMPC (Secure Multi‑Party Computation) design, shifting trust from a limited number of validator nodes to a broader network. In the long term, it can further adopt FHE (Fully Homomorphic Encryption), enabling arbitrary computation directly on encrypted data without decryption, pushing privacy computation toward a true “zero‑trust” model.
Those who wish to understand the implementation details of MPC on this payment‑oriented chain may refer to the BenFen official whitepaper.
Why Is MPC Architecture Important?
In real‑world scenarios involving stablecoin payments and cross‑border settlements, users demand experiences that approach Web2 in speed and convenience while still offering the security and privacy guarantees of blockchain‑layer systems. Design paths like BenFen’s demonstrate that by nativizing MPC at the protocol layer, it is possible to overcome the performance drawbacks of traditional privacy schemes and bring secure multi‑party computation from the lab to large‑scale commercial payments.
Conclusion
MPC is reshaping the underlying logic of blockchain: shifting from “public transparency” toward “verifiable privacy.” Future competition in blockchain will no longer focus solely on TPS or ecosystem size, but on achieving an optimal balance among privacy, performance, and verifiability.
From today’s development trajectory, multi‑party computation blockchains built around MPC are becoming a key solution to this problem. And reference designs like BenFen’s chain‑layer integration define a new paradigm for scalable, privacy-preserving payment infrastructure on blockchain.
I love how MPC takes blockchain privacy to the next level. The ability to run computations without revealing private data is game-changing, particularly in finance. Do you think this will eventually replace traditional encryption methods, or is it more of a complementary tool?